Bitcoin is a relatively new form of currency that is really beginning to hit the mainstream, but many people still don’t understand its significant value, and why they should make the effort to use it, both for their own benefit and that of humanity in general. In this post, Dream Foundation founder Philip Agyei Asare will identify some top 10 questions about Bitcoin to give you a clearer understanding of what it is, what it does, and how you can use it to buy products or services online.
1. What Is Bitcoin? Any discussion of Bitcoin must be preceded by an explanation of what the Blockchain is, since Bitcoin is the currency of the Blockchain, in much the same way that the dollar is the currency of the United States, or email is a communications mode of the internet. The Blockchain is the public ledger that documents all confirmed Bitcoin transactions, and therefore offers a platform of virtually limitless algorithms that support all of the transactions on the blockchain. Since it consists of mathematics, it is incorruptible, unlike the existing centralized currency systems of the world, that rely on human transaction “verification”. Mathematics can be trusted to be true, but as we have found out, banking cannot be trusted to be true, or supportive of its users’ best interests. Bitcoin (BTC) is a form of currency that is digital; that is, it does not consist of physical notes and coins and instead exists as a solved logarithm on the Blockchain. In this era of Internet and digitization, we’ve moved from phone to VoIP calls, face-to-face meeting to video conferencing, fax to email, cable television to IP TV, and now Bitcoin joins this growing list of advancements.
2. Who Developed The Idea Of Bitcoin? The concept of the Blockchain and Bitcoin was developed by Satoshi Nakamoto, who resides in mysterious anonymity. Investigations as to his real identity have been extensive and intense, and there are only scattered clues. For example, he is said to be from Japan, but Bitcoin software was not originally available in Japan, and his mail ID was from Germany. He developed the system and the Bitcoin software (that is used to run the system) in 2009, but disappeared into seemingly thin air in 2010, apparently after he saw that Bitcoin was well on its way to development and adoption. The other developers of the system stopped hearing from him in 2010, and since then, plenty of entertaining speculation about his real identity has occurred. For example, it was suggested that his name was just a mashup of popular Japanese companies — SAmsung TOSHIba NAKAmichi MOTOrola. But what he created was definitely the joyful fantasy of every tech guy in the world, and clearly Bitcoin was his gift to the world.
3. What Is So Special About the Bitcoin System? Bitcoin is a system which enables anonymous currency transactions: the identification of the persons making such transactions will remain anonymous, and cannot be traced back At the same time, each transaction is verified and recorded publicly on the Blockchain (as explained above, basically, the hosting platform upon which Bitcoin functions) and once confirmed cannot be reversed or tampered with. The fact that the Blockchain is a public ledger makes transactions witnessed and verified by all users. Satoshi purposely designed his system to be de-centralized and a peer-to-peer network. Thus, it is not controlled by any central authority – unlike the current centrally controlled banking system in which the people are at the mercy of its policies and practices. Instead, because it is comprised of the growing millions of users, increasing daily, each of whose computers is a node of the whole system, this giant de-centralized network of computers is in the hands of the People. Likewise, it is run by a worldwide network of brilliantly innovative programmers and developers, contributors, and freedom enthusiasts who contribute their time, talent and energy to the Blockchain and Bitcoin. Essentially, Satoshi Nakamoto gave to the people of the world a system of currency, communication and exchange which makes possible independence from the corrupt and destructive central banking system, by simply replacing it with the Blockchain and Bitcoin. While attempts at crypto currencies were unsuccessfully tried for years prior to Satoshi Nakamoto, he not only created a successful replacement for central banking, he was so talented that he even solved the previously long-standing problem of double spending of digital currency which had plagued those early attempts.
4. What is Double Spending? We can make many copies of digital data, and abuse that ability; e.g. people copy software and sell it as counterfeit or pirated copies. In the same way, because BTC is digital currency, any merchant or transactor could run the risk that the payer (the holder of that digital token BTC) could copy the BTC, send one copy as payment and retain the other still in his possession, thus enabling double spending of the same BTC. However, because of Satoshi Nakamoto’s brilliant design, every BTC transaction must be verified and publicly posted on the Blockchain to be spent, thus solving the double spending dilemma, as follows. The Blockchain retains a list of all BTC created, using the complex unique identification number which is automatically generated for each newly created BTC. Whenever a new transaction is made, its validity is checked by confirming from that list that the BTC was not used before. Thus, no one can copy the currency and use it for more than one time. It’s a brilliantly simple and effective idea to stop even the possibility of double spending Bitcoin.
5. How Does A Public Listing Make Things Anonymous? The public listing only shows the transaction ID and the amount of currency transferred. The user is anonymous in the system because you don’t provide any of your personal details like your name, address, email, phone number, etc. that is required identifying information in the existing central banking system, like when using payment gateways like Paypal, credit cards, etc. When using Bitcoin, your personal information is sacrosanct, by intention and design.
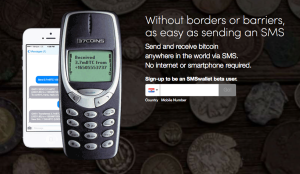
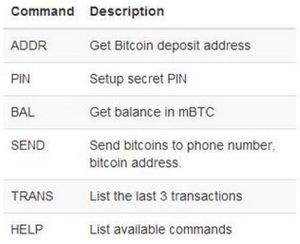
6. How do you use Bitcoins? Bitcoin are kept in a digital wallet which you create easily online, and can keep on your computer, or on a website online, which will manage and secure your wallet for you. If you follow Bitcoin news and activities, you will have heard that sometimes Bitcoin are stolen from wallets by hackers. While this is infrequent and very difficult to do, (like bank robberies or hacking of the central banking system by criminals) unlike the current central banking system, you can totally safeguard against this possibility by simply storing your wallet(s) on a computer which is not connected to the internet. This will therefore exclude the possibility of having it accessed and hacked. You can then transfer BTC from your stored wallet to a computer with internet access only for the short period of time needed to transact any purchases, and then restore the balance in your wallet to your offline computer for safe storage until your next purchase. And you can also have as many wallets and Bitcoin addresses (where you receive money from others) as you like. What’s more, you can use Bitcoin software on top of Tor to prevent anyone from tracking your IP address – total anonymity guaranteed!
7. How many people are using this new Bitcoin system? At this very moment, more than 10 million Bitcoin are in existence, which currently converts to 207.929 million USD worth! In one day, more than 45,000 transactions of a total of 2.5 million BTC (48.5 million worth of USD) is handled by the Bitcoin network. To get an idea of the considerable and fast-growing acceptance of Bitcoin use around the world, you can review the information on the report issued at the end of July 2014 entitled The State of Bitcoin, here: http://www.slideshare.net/CoinDesk/state-of-bitcoin-q2-report
8. How Do I Acquire Bitcoin? Getting and using Bitcoin is easy. There are various ways to get Bitcoin: · ‘Mining’ · Currency exchange (bitcoin in return for Dollars or Euros) via Bitcoin provider services like Coinbase, etc. · Providing services to others in return for Bitcoin
9. What’s Mining? Mining is the process of extracting Bitcoin currency from the Blockchain by using hardware specifically designed to solve the necessary logarithms, which then generate BTC. Whenever a new logarithmic block is thus “found” by such mining equipment, its owner is gifted with 50 Bitcoins. The capability of mining equipment to so solve the necessary logarithms on the Blockchain is referred to as hashing power, and the necessary hashing power required to solve each subsequent logarithm on the Blockchain likewise increases with each successful mining of BTC. Bitcoin mining itself is a business, since most people involved in BTC mining do so to gain profit by generating BTC which can then be sold, traded or used for purchases.
10. How Do You Spend A Bitcoin? Bitcoin is used in all the same ways that traditional “currency” is used: BTC can be sent to a person, to a merchant to buy goods or services, or to make donations to non-profit foundations who accept BTC (a growing list), such as Wikileaks, Wikipedia, WantToKnow.info, Dream Foundation Ghana, etc. To send to a private party, you only need their Bitcoin address. To pay for merchandise, you simply use the payment platform set up by Hey, Nana merchants that accept Bitcoin, like merchants who accept PayPal payments do now. This is one of the implementations that Dream Foundation is planning to put in place in Ghana and beyond. I will be putting out other articles explaining the new people’s world of Bitcoin and the Blockchain further, and in the interim, I welcome any questions you may have, which can be sent to the following email address: drimin99@gmail.com or ceo@paksmsgh.com or philip@dreambitcoinfoundation.org